List of threats that Yandex Browser protects your computer against
Yandex Browser automatically collects data about unwanted software in your OS and offers to delete it. Gathering statistics helps your browser detect if you have unwanted software in your system. These statistics do not infringe on your data privacy.
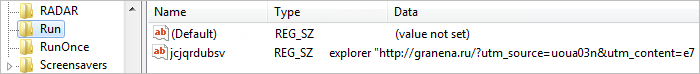
Modified system launch parameters (StartPage)
Unwanted software adds an address to the system registry for an advertising site that imitates a popular online service. The key containing the address is added to the section where legal software is registered for auto-start.
As a result, whenever you restart your computer, your default browser opens the advertised site.
Driver filter that displays unwanted content (Fake NetFilter)
The Driver filter intercepts internet traffic to display intrusive and disturbing ads in the browser, open ad tabs, send users to unwanted sites, and steal their personal data.
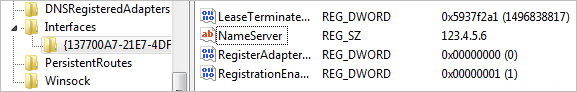
DNS substitution (Infected DNS)
An unwanted program changes DNS settings.
Normally, when a user opens a web page, the browser sends a request with the specified domain to a special DNS server. This DNS server sends the corresponding IP address in the response.
Unwanted software replaces the DNS server address in the system settings. As a result, all requests are sent to a different server, which will redirect users to fraudulent, phishing, or advertising sites.
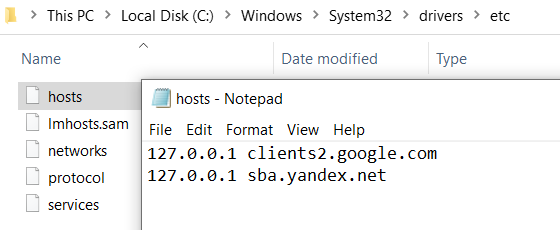
Infected Hosts
The hosts system file located in the C:\Windows\System32\drivers\etc folder contains a list of website domain addresses and their corresponding IP addresses. Malicious programs can write fake addresses to the hosts file, block access to popular sites, redirect users to phishing pages, or disable browsers' security functions.
Unwanted browser extensions
The program installs malicious extensions that open advertising tabs, display intrusive or disturbing ads, or steal user's personal data without the user's knowledge.
Antivirus programs are not very good at recognizing malicious extensions. This is because all extensions operate within a browser and do not affect the computer’s operating system.
We recommend installing extensions from the Opera Add-ons or Chrome Web Store online stores, where extensions are checked to ensure they're safe.
Unwanted software that modifies traffic (PBot)
The unwanted program launches every time an infected computer is turned on and tracks apps that the user launches. When the user opens one of the browsers, the malicious software embeds its code in the browser process to redirect the user to an advertising or phishing page, change their default search settings, and steal the user's personal data.
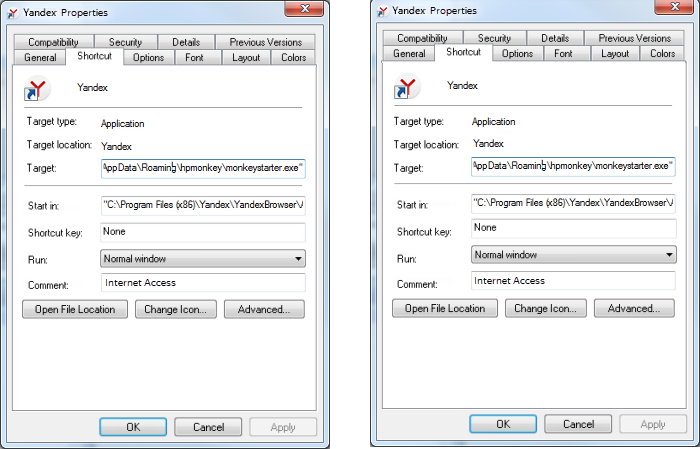
Browser shortcut modification (Infected LNK)
The unwanted program changes the browser launch shortcut by adding additional parameters (usually a site address) or launches another app instead of the browser. As a result, each time you launch the browser, it displays ad pages.